Cyber Threat Protection for Government Macs
Protecting government Macs from cyber threats has gotten complicated with all the attack vectors, security tools, and compliance requirements flying around. As someone who has defended federal Mac deployments against real threats, I learned everything there is to know about keeping Apple hardware secure. Today, I will share it all with you.
Here’s what generic security advice misses: government Macs face different threat profiles than consumer devices. Nation-state actors, targeted phishing, and persistent threats require different defenses.
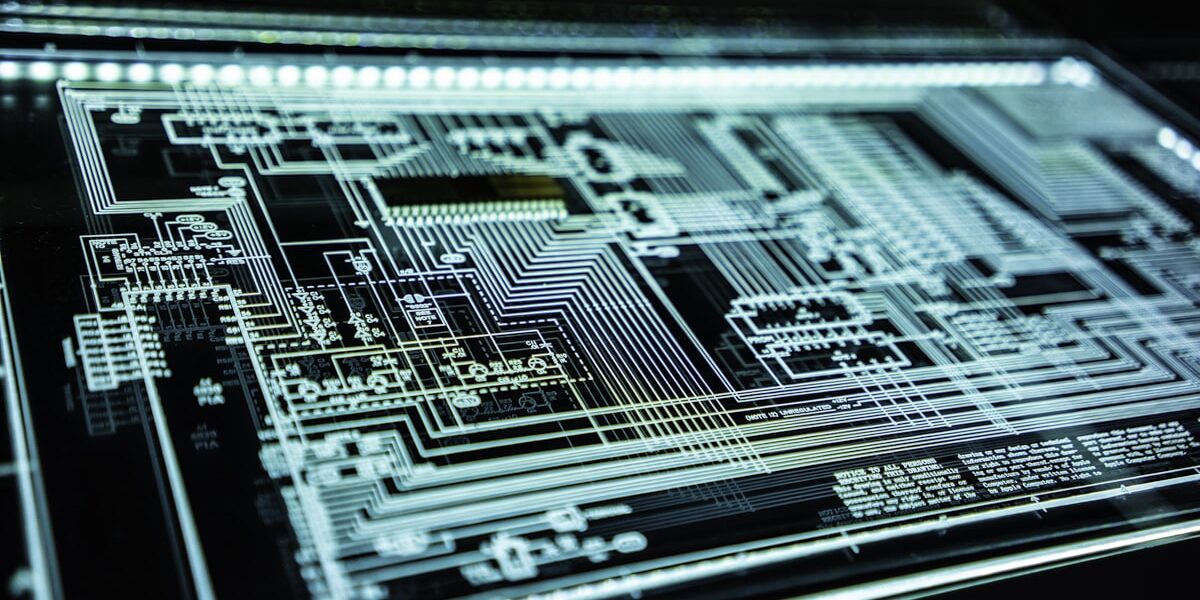
Built-in Protections
Probably should have led with this section, honestly. macOS includes XProtect malware detection, Gatekeeper app verification, and System Integrity Protection. These provide baseline defense when properly configured.
Endpoint Protection
That’s what makes enterprise security software valuable for us government IT folks—additional detection capabilities beyond built-in tools. Choose products certified for government use.
User Awareness
Phishing remains the most common attack vector. Train users to recognize suspicious emails, links, and attachments. Regular reminders and simulated phishing tests reinforce awareness.
Network Defenses
Firewalls, intrusion detection, and secure DNS add network-layer protection. Monitor for suspicious traffic patterns that might indicate compromise.
Incident Response
Have plans ready before incidents occur. Know who responds to what. Practice procedures. Preserve evidence during response.