How to Set Up CAC Card on Mac for the First Time
CAC setup on Mac has gotten complicated with all the conflicting advice flying around. Ask five people in your unit how they did it and you’ll get five different answers — half of which probably don’t apply to your macOS version anyway. As someone who spent two hours on hold with IT and another hour doing trial-and-error on a government-issued MacBook Pro, I learned everything there is to know about getting a CAC card working on Mac from scratch. Today, I will share it all with you.
The order matters here. Skip a step, do two of them backwards, and you’ll hit a wall that looks completely unrelated to the thing you actually broke. So, without further ado, let’s dive in.
What You Need Before You Start
Probably should have opened with this section, honestly. Pull everything together before you download a single file.
- A government-issued CAC card. Nothing else on this list matters without one.
- A PIV-compliant USB CAC reader. Identiv and HID are the brands you’ll see most in government spaces. Avoid the generic $8 readers on Amazon — they cause problems that are genuinely hard to diagnose.
- macOS 11 or later. Apple Silicon (M1, M2, M3) and Intel Macs both work. They may need different driver versions. Write that down now.
- Admin access to your Mac. If your machine is managed by your department’s IT, you may need to request elevated rights before starting. Don’t assume.
- Your exact macOS version number. Go to Apple menu > About This Mac. Write down every digit — not “Ventura,” but “13.4.1” or whatever it says. Installing middleware built for 13.3 on a 13.5 machine is the number one first-timer mistake. Don’t make my mistake.
Install the Right Middleware for Your Mac
But what is middleware? In essence, it’s the translator between your CAC card and your Mac. But it’s much more than that — without it, plugging in your reader does exactly nothing. Your computer just sees a USB device and moves on.
Most government users run OpenSC or Identiv middleware. OpenSC is free and open-source. Identiv is proprietary, roughly $0 to you personally, and widely deployed across DoD environments. Both work on Mac. ActivClient is also out there — use it only if your command specifically mandates it.
Here’s the sequence:
- Plug your CAC reader into a USB port. Your Mac will recognize it as a device. It won’t do anything useful yet. That’s fine.
- Visit the official middleware download page for your organization, or use the DoD-recommended repository. If you’re not sure which middleware your agency runs, call your helpdesk and ask directly. Do not guess.
- Download the .pkg or .dmg installer that matches your exact macOS version and chip type — Apple Silicon or Intel. I’m apparently someone who skips this check instinctively, and downloading the wrong version cost me 30 minutes of troubleshooting a completely broken installation. Verify before you click download.
- Double-click the installer, follow the prompts, enter your admin password when asked. Let it finish without interrupting it.
- Restart your Mac when prompted. Not later. Now.
- After the restart, open Terminal — Applications > Utilities > Terminal. Plug in your reader and type
sc-hsm-tool --listor check your system logs. If the reader shows up, you’re good. If it doesn’t, go back and verify the middleware version matches your macOS release exactly.
That’s what makes middleware setup the step that catches everyone. It looks simple until the version mismatch bites you at the worst possible moment.
Trust the DoD Root Certificates
Most guides skip this step. Most people who follow those guides hit a wall an hour later and have no idea why. Your Mac needs to trust the certificate chain that signed your CAC — and that chain starts with a DoD root certificate sitting in your Keychain.
When you try to log in with your CAC, the system validates the entire trust chain from your card’s certificate all the way back to the DoD root. No trust at the root level means the login fails — usually with a vague, unhelpful error message that sends you looking at the wrong thing entirely.
- Visit the official DoD PKI repository and download the root certificate bundle. It’s typically named something like
dod-ca-certs.p7b. - Double-click the bundle. Keychain Access will open and ask which keychain to use — choose “System,” not “Login.” Enter your admin password.
- Open Keychain Access manually (Applications > Utilities > Keychain Access) and search for “DoD” to find what you just imported.
- Find the DoD Root CA certificate and double-click it.
- Click the Trust dropdown and set it to “Always Trust.” Close the window. Enter your admin password again when prompted.
One thing worth knowing: major macOS upgrades sometimes reset certificate trust settings. Going from macOS 13 to 14? Plan to repeat this entire import process afterward. Apple does that. It’s annoying. Now you know.
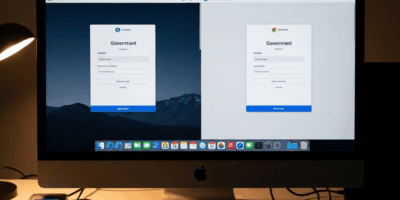
Configure Your Browser to Read the CAC
Your browser is the final link. It needs to know how to ask your reader for the right certificate when a .mil site demands authentication. Safari and Chrome handle this differently — almost frustratingly so.
For Safari: Safari reads directly from your system Keychain. Plug in your reader, visit a .mil or government site, and Safari will detect your certificate automatically and prompt you to select it. No manual configuration needed. Honestly the easiest path if your agency allows it.
For Chrome: Chrome is more particular about this. You’ll need to register the PKCS11 module your middleware installed.
- Open Chrome and navigate to
chrome://settings/certificates. - Click the “Security Keys” tab.
- Under “Manage Module,” click “Add Module.”
- Navigate to your middleware’s PKCS11 file. For OpenSC, it’s usually at
/usr/local/lib/opensc-pkcs11.so. For Identiv, check your installation folder — it won’t be in the same place. - Select the file, click “Add,” and confirm Chrome acknowledges the module loaded.
- Restart Chrome. Try a government login page. Chrome will now see your CAC.
Firefox is a whole separate situation — I’ve got a dedicated guide for that. For now, Safari or Chrome covers the vast majority of government Mac setups.
Test Your CAC Login and Fix Common First-Time Errors
Navigate to a government test site — MilConnect works, or a .mil OWA portal, or your agency’s internal login page. Plug in your reader. Hit “Login” or “Select Certificate.”
One of three things happens next.
Success: A certificate selection dialog appears. Your name is on it. Click your cert, enter your 6-digit CAC PIN, and the page loads. You’re done. That’s what it feels like when everything is right.
Error — Reader Not Detected: Your browser can’t see the reader at all. First check the obvious: is it physically plugged in? Is the light on? Try a different USB port — some government-issue Macs with USB-C adapters are genuinely finicky about this. Still nothing? Go back to middleware, verify you installed the version that matches your macOS chip and release number, and re-run the Terminal detection test. If it still won’t show, call IT. A silent middleware installation failure is hard to diagnose without log access.
Error — Certificate Not Trusted: Your browser sees the certificate but your Mac won’t accept it. Almost always means the DoD root certificate import didn’t stick, or the trust setting was never applied. Open Keychain Access, find the DoD Root CA, double-click it, and re-apply “Always Trust.” Save it, restart your browser, try again.
Error — PIN Prompt Never Appears: The browser found your certificate but isn’t asking for your PIN. In Chrome, this usually means the PKCS11 module registration didn’t complete. Redo that step. In Safari, restart the browser and try again. If neither works — restart the whole Mac and test fresh. Sometimes the middleware needs a full reboot to settle.
When it clicks, you’ll know immediately. The login goes through, the page loads, and you’re in. Next time someone in your office asks how to do this, you’ll walk them through it in five minutes instead of spending an afternoon on hold.



Stay in the loop
Get the latest apple mac in government updates delivered to your inbox.